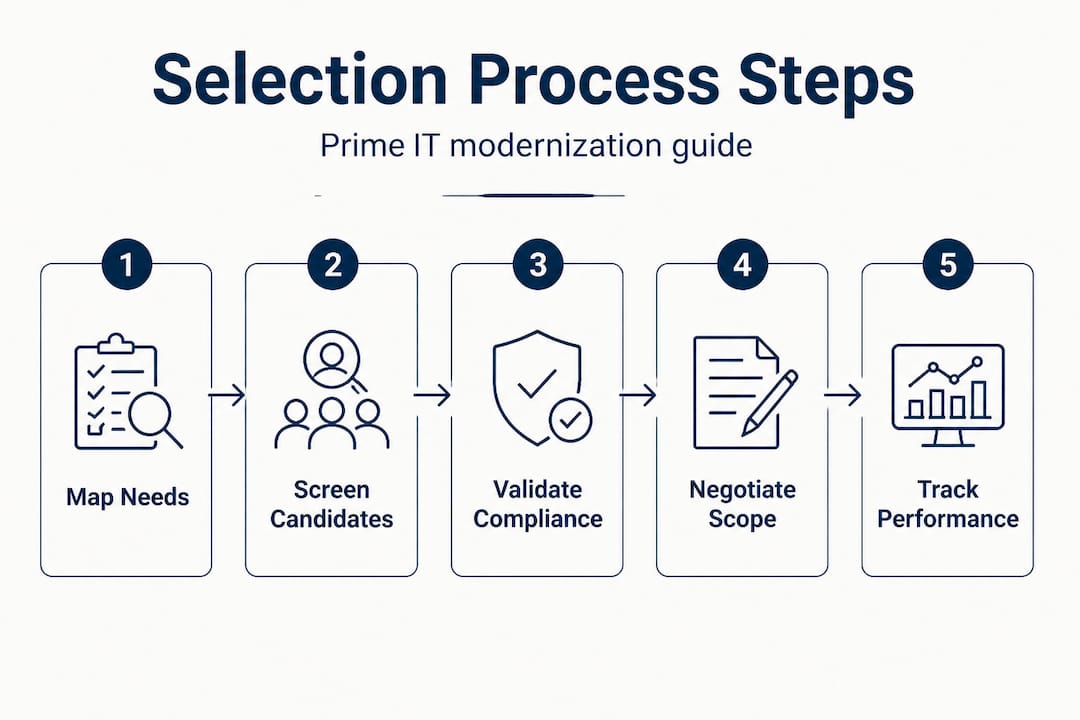
Prime contractors managing complex government IT programs face a precise and unforgiving challenge: identify subcontracting partners who can perform, prove compliance, and survive contracting officer scrutiny, all before a proposal goes out the door. The margin for error is narrow. Selecting the wrong partner delays delivery, triggers audit exposure, and damages past performance ratings. This guide provides a structured, step-by-step framework covering compliance prerequisites, candidate screening, risk validation, scope negotiation, and performance management, giving prime contractors a repeatable process for building teams that hold up under federal oversight.
Table of Contents
- Understanding requirements and prerequisites
- Decomposing work packages and screening candidates
- Validating compliance, risk controls, and capacity
- Negotiating scope, deliverables, and performance management
- Why relationship-driven teaming often backfires in public sector IT
- Connect with prime-ready IT modernization partners
- Frequently asked questions
Key Takeaways
| Point | Details |
|---|---|
| Map requirements first | Start by decomposing your statement of work and compliance demands to set the selection process up for success. |
| Screen objectively | Use measurable past performance and regulatory literacy as the foundation for evaluating subcontractor candidates. |
| Validate risk controls | Document the risk controls, financial capacity, and compliance history of candidates to withstand CO scrutiny. |
| Negotiate with metrics | Define clear, measurable scope, deliverables, and CPARS-style evidence for long-term performance management. |
| Avoid relationship bias | Choose teaming models based on solicitation and outcome needs, not pre-existing relationships. |
Understanding requirements and prerequisites
Building on the high-level stakes, the compliance and policy foundation must be clear before any partner selection begins. Federal subcontracting is governed by specific regulatory clauses, and overlooking them early creates problems that are expensive to fix mid-program.
Subcontracting compliance is governed by both SBA guidance and FAR requirements, specifically FAR 52.219-9 and FAR 52.244-2. FAR 52.219-9 requires prime contractors on large contracts to develop a written subcontracting plan with specific goals for small business participation. FAR 52.244-2 governs purchasing systems and the consent-to-subcontract process, meaning the contracting officer (CO) has explicit authority to review and approve or disapprove certain subcontracting decisions.
Consent-to-subcontract requirements drive how primes treat different subcontracts as higher or lower risk. Not every subcontract triggers formal CO consent, but complex, high-value, or sensitive IT work often does. Primes who misread these thresholds create avoidable compliance gaps.
Key prerequisites to address before sourcing any partner include:
- Subcontracting plan obligations. Confirm whether the prime contract requires a formal subcontracting plan with small business goals. If so, the plan must be approved before award.
- Consent thresholds. Identify subcontracts likely to require CO consent based on value, technical complexity, or risk profile. Document your determination in writing.
- SBA SUBNet. The SBA's SUBNet database is a structured sourcing tool for identifying small business subcontractors. Using it signals good-faith compliance effort to COs.
- Purchasing system review readiness. If the prime operates under a government-approved purchasing system, subcontracting practices are subject to periodic government review. Gaps in documentation surface during those audits.
| Requirement | Regulatory basis | Trigger condition |
|---|---|---|
| Subcontracting plan | FAR 52.219-9 | Large contracts with subcontracting opportunities |
| Consent to subcontract | FAR 52.244-2 | High-value, complex, or sensitive subcontracts |
| SUBNet sourcing | SBA policy | Small business participation goals |
| Purchasing system review | FAR Part 44 | Approved purchasing system holders |
"Map your statement of work to the risk and review requirements before issuing any subcontract. Doing this early prevents compliance gaps that are difficult to close after award."
Pro Tip: Before any candidate outreach, review the solicitation's required representations and certifications. Some government programs restrict subcontracting to specific business types or require documentation of socioeconomic status, such as SDVOSB or SBA-certified designations. For broader context on structuring these partnerships, the IT modernization partnership guide provides useful framing. Understanding public sector IT contracting requirements in depth helps primes avoid surprises during proposal review.
Decomposing work packages and screening candidates
With requirements defined, structuring work packages before evaluating candidates produces a more objective and defensible screening process. Rushing to candidates before decomposing the statement of work results in poorly scoped subcontracts and misaligned performance expectations.
Step-by-step work decomposition process:
- Identify distinct technical functions. Break the overall technical approach into discrete functional areas, such as cloud migration, DevOps pipeline setup, compliance automation, or data analytics integration. Each function becomes a candidate work package.
- Assess risk and complexity per package. Some packages carry greater compliance sensitivity, integration risk, or delivery complexity than others. Label each accordingly. Higher-risk packages may require CO consent and deserve more rigorous candidate screening.
- Define measurable deliverables per package. Avoid loose scope definitions. Each package should have clearly stated outputs, timelines, and acceptance criteria before you approach any candidate.
- Determine subcontract type suitability. Not every package suits a fixed-price arrangement. Packages with evolving requirements may call for time-and-materials or cost-reimbursement structures.
- Match package characteristics to candidate profile requirements. Once packages are defined, build a required capabilities list for each, including technical tools, certifications, clearances if applicable, and similar-scope delivery experience.
Candidate screening should then be objective and measurable. CPARS evaluations are required to be supported by objective data, meaning performance ratings on past federal contracts carry documented weight. Pull CPARS records early to verify past ratings across cost, schedule, and technical performance categories.
| Screening criterion | Primary sourcing tool | What to look for |
|---|---|---|
| Past performance ratings | CPARS | Green or better across prior evaluations |
| Socioeconomic certifications | SAM.gov / SBA | SDVOSB, SBA-certified, WOSB designations |
| Technical capabilities | SUBNet / capability statements | Relevant tool sets, certifications, past scope |
| Financial stability | Dun & Bradstreet / references | Positive credit indicators, no debarment |
| Similar scope experience | Proposals, case studies | Demonstrable outcomes on comparable programs |
Key screening filters to apply at this stage:
- Scope similarity. A candidate who delivered cloud migration for a single state agency is a stronger fit for an equivalent scope than one claiming broad cloud familiarity without demonstrated delivery.
- Compliance literacy. Government IT modernization programs involve regulatory regimes such as FedRAMP, FISMA, and state-specific frameworks. Candidates who already operate within these frameworks require less oversight.
- Outcome focus vs. staff augmentation. Candidates who own clearly defined scopes and manage their own delivery are lower-risk than those offering primarily staff augmentation, which transfers delivery risk back to the prime.
Pro Tip: Use SBA SUBNet search filters combined with CPARS historical data to create a short list of three to five qualified candidates per work package before scheduling any conversations. This protects you from selection bias toward familiar names.
The public sector partnering guide offers additional frameworks for evaluating candidate types. For primes who need partners that are already prepared for award-ready engagement, the contract-ready partnership overview is worth reviewing.
Validating compliance, risk controls, and capacity
After initial screening, validating each candidate's compliance literacy, risk management practices, and actual delivery capacity is the step that most often separates strong subcontractors from those who appear strong on paper.
Consent-to-subcontract requirements become more stringent for higher-risk, higher-complexity, or higher-value subcontracts. This means that for IT modernization programs involving sensitive data, legacy system integration, or mission-critical infrastructure, primes face a higher documentation burden when justifying subcontractor selection to the CO.
Validation should cover three dimensions:
1. Regulatory and security compliance literacy
- Does the candidate understand FedRAMP authorization requirements, particularly if the work involves cloud services accessible to federal data?
- Can they demonstrate existing controls aligned to NIST SP 800-53 or similar frameworks?
- Do they maintain documentation, such as System Security Plans or Authority to Operate records, that can be referenced in the proposal?
2. Risk management and audit readiness
- Does the candidate maintain its own quality control plan and risk register?
- Have they operated under government oversight, including CO reviews or inspector general audits, without findings?
- Can they provide evidence of incident response procedures and change management processes?
3. Financial, workforce, and delivery capacity
- Does the candidate have sufficient bonding capacity, cash flow, and working capital to sustain performance through government payment cycles, which can average 30 to 60 days?
- Is the technical workforce stable, or does the candidate rely heavily on contingent labor that creates delivery continuity risk?
- Does the candidate have experience managing subcontract performance at the scale required by this program?
A useful practice is to score each candidate across these three dimensions using a structured assessment matrix. Weight scores according to the risk profile of the work package.
Statistic to note: Contracting structures should be driven by solicitation requirements rather than relationship preferences. This principle is especially critical at the validation stage, where familiarity with a candidate can create blind spots around genuine compliance gaps.
Pro Tip: Document your validation findings in a standardized format and retain them in your contract management system. If a CO requests justification for your subcontractor selection, having dated, structured records is far more defensible than verbal explanations after the fact.
For building strategic IT partnerships with the right risk profile, validation documentation is not just a compliance formality. It is the evidence base that supports a resilient, auditable team structure. The resources at successful IT partnerships elaborate on how validation processes support long-term program performance.
Negotiating scope, deliverables, and performance management
Once compliance and capacity are validated, the focus shifts to defining the working relationship in terms that are clear, measurable, and enforceable. Vague subcontracts are one of the most common sources of cost overruns and schedule slippage in public sector IT programs.
Negotiation and scope definition steps:
- Write the scope of work before the subcontract agreement. The scope document should define specific deliverables, acceptance criteria, reporting cadence, and escalation procedures. Do not negotiate price before scope is finalized.
- Establish measurable performance standards. Each deliverable should have a defined quality metric. For a DevOps pipeline engagement, for example, define what constitutes a complete pipeline, what automated testing coverage threshold is required, and what deployment frequency is acceptable.
- Conduct a price and cost reasonableness analysis. FAR subcontracting requirements obligate primes to ensure cost reasonableness. Collect at least two comparable market data points or use established labor category rates from published sources.
- Include FAR consent provisions explicitly. If the subcontract is subject to CO consent, reference that requirement in the subcontract agreement and include a condition that work cannot commence until consent is received.
- Build a performance management plan. Define how performance will be tracked across the life of the subcontract, including schedule milestones, deliverable review cycles, and issue resolution processes.
| Management element | Best practice | Risk if omitted |
|---|---|---|
| Scope definition | Written, measurable, pre-negotiation | Scope creep, disputed deliverables |
| Cost reasonableness | Market data or published rates | FAR compliance exposure |
| CPARS integration | Subcontractor data in description field | Incomplete past performance record |
| Milestone tracking | Formal review cycles | Schedule slippage undetected |
| Consent documentation | Written CO approval retained | Audit findings, disallowed costs |
CPARS guidance specifies that in prime-subcontractor relationships, evaluations are conducted on the prime, with relevant subcontractor information captured in the description field. This means every prime contractor is accountable for what its subcontractors deliver.
Planning for CPARS-style performance management from day one, rather than treating it as an end-of-program exercise, produces a stronger evaluation record. Primes who actively document subcontractor contributions throughout performance are better positioned to defend their ratings and use those ratings as evidence of past performance in future proposals.
For a deeper look at managing multi-partner IT projects at scale, a structured performance management approach is the common thread across high-performing programs. Understanding prime contractor roles in the context of subcontract accountability reinforces why scope clarity is not optional.
Why relationship-driven teaming often backfires in public sector IT
There is a persistent pattern in federal IT teaming: primes default to familiar partners because past collaboration feels like a proxy for future performance. It is an understandable instinct. Shared vocabulary, established communication patterns, and mutual trust lower the friction of early program setup. But in public sector IT modernization, that instinct frequently produces the wrong outcome.
Contracting structures must be driven by solicitation requirements, not relationship preference. When a team is built around familiarity rather than solicitation mapping, capability gaps tend to surface during technical evaluation or, worse, during delivery. A trusted partner who lacks FedRAMP experience, for example, is still a compliance liability regardless of relationship depth.
The audit exposure dimension is equally significant. COs who review subcontractor selection documentation are not evaluating the quality of relationships. They are evaluating whether the prime followed a sound, documented process for identifying and selecting qualified partners. A selection decision that cannot be traced to objective capability evidence and regulatory compliance review is difficult to defend. The documentation either exists or it does not.
The harder lesson, confirmed repeatedly across government IT modernization programs, is that rigorous process produces more resilient teams than familiarity does. Partners selected through objective screening, compliance validation, and scope-aligned negotiation tend to perform more consistently under oversight because they were chosen for the right reasons.
Primes who want to build defensible, outcome-driven teams should treat partner selection as a structured acquisition process, not a staffing decision. This perspective also applies to multi-partner project management, where the rigor applied at selection time determines how much coordination overhead the prime carries throughout delivery.
Connect with prime-ready IT modernization partners
Streamlining the partner selection process becomes significantly easier when the candidate pool is already pre-qualified for public sector compliance, outcome accountability, and scope ownership. Rutledge & Associates is an SDVOSB, woman-owned, SBA-certified digital systems firm that specializes in government IT modernization through cloud-native re-architecting, DevOps pipelines, compliance automation, and real-time analytics. Primes can explore vetted prime-ready IT partners who own clearly defined scopes with minimal oversight requirements. For programs specifically targeting state and local government in the mid-Atlantic region, the Maryland IT modernization partners directory provides a starting point for outcome-focused teaming conversations.
Frequently asked questions
What are the key compliance requirements for public sector IT partner selection?
Prime contractors must follow FAR 52.219-9, FAR 52.244-2, and SBA subcontracting guidance for compliant selection and documentation, including subcontracting plans and consent-to-subcontract procedures.
How do contracting officers evaluate the suitability of subcontractors?
COs review risk, compliance documentation, and performance metrics to assess alignment with policy. Consent-to-subcontract reviews require primes to demonstrate sound business judgment in partner selection.
How can primes demonstrate past performance when teaming with new partners?
Primes should include CPARS-supported objective data in proposals and track subcontractor contributions throughout performance to build a credible, documented record for future evaluations.
When does the consent-to-subcontract requirement apply?
Consent is typically required for higher-risk or complex subcontracts. Primes should verify applicable thresholds in FAR Part 44 and seek CO guidance when scope, value, or sensitivity is elevated.
What are common mistakes in partner selection for IT modernization?
Selecting partners based on relationships rather than solicitation-driven criteria is the most common error, leading to technical misalignment, compliance exposure, and poor audit defensibility.
